- User Account Control User Oobe Create Elevated Object Server
- What Is User Oobe
- Oobe Screen Windows 10
- Microsoft Oobe Process
- User Oobe Create Elevated Object Server Virus
- Intune User Oobe Create Elevated Object Server
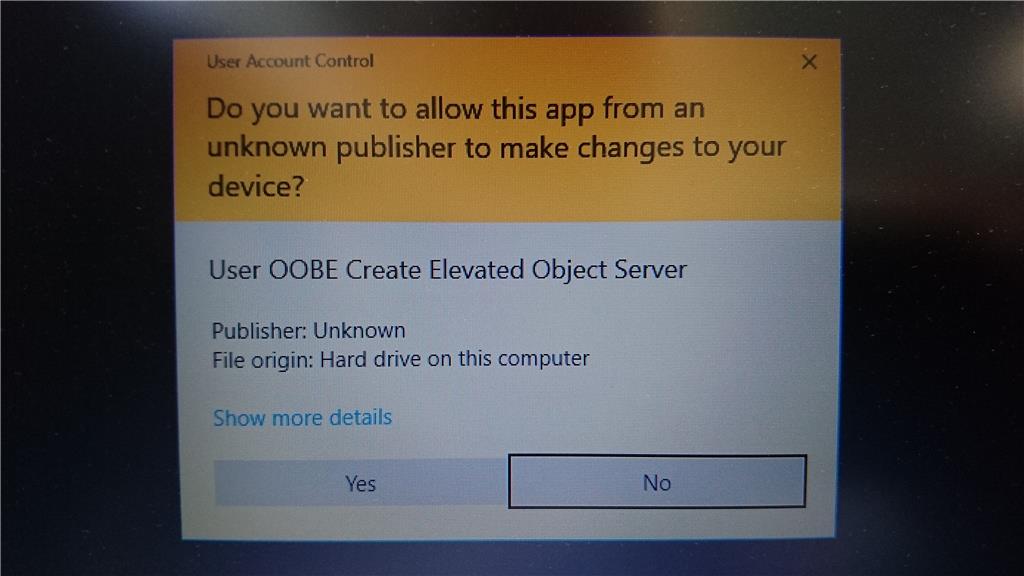
If Azure Image Builder creates a Windows custom image successfully, and you create a VM from it, then find that the VM creation fails or does not complete successfully, you will need to review the Windows Server Sysprep documentation or raise a support request with the Windows Server Sysprep Customer Services Support team, who can troubleshoot. When I try to add a new user a User Account Control (UAC) popup asks if I want to allow 'User OOBE Create Elevated Object Server' app to make changes to my computer. The UAC box also says 'Verified Publisher: Microsoft Windows' I haven't yet made any other users on this Windows 10 Pro installation. What we did to create the image was create a HyperV, install all our software etc on it and then somehow uploaded it to the SCCM server and distributed it. I wasn't involved in the beginning part of the config so I don't know how to do it.
The COM elevation moniker allows applications that are running under user account control (UAC) to activate COM classes with elevated privileges. For more information, see Focus on Least Privilege.
When to Use the Elevation Moniker
The elevation moniker is used to activate a COM class to accomplish a specific and limited function that requires elevated privileges, such as changing the system date and time.
Elevation requires participation from both a COM class and its client. The COM class must be configured to support elevation by annotating its registry entry, as described in the Requirements section. The COM client must request elevation by using the elevation moniker.
The elevation moniker is not intended to provide application compatibility. For example, if you want to run a legacy COM application such as WinWord as an elevated server, you should configure the COM client executable to require elevation, rather than activating the legacy application's class with the elevation moniker. When the elevated COM client calls CoCreateInstance using the legacy application's CLSID, the client's elevated state will flow to the server process.
Not all COM functionality is compatible with elevation. The functionality that will not work includes:
- Elevation does not flow from a client to a remote COM server. If a client activates a remote COM server with the elevation moniker, the server will not be elevated, even if it supports elevation.
- If an elevated COM class uses impersonation during a COM call, it might lose its elevated privileges during the impersonation.
- If an elevated COM server registers a class in the running object table (ROT), the class will not be available to non-elevated clients.
- A process elevated by using the UAC mechanism does not load per-user classes during COM activations. For COM applications, this means that the application's COM classes must be installed in the HKEY_LOCAL_MACHINE registry hive if the application is to be used both by non-privileged and privileged accounts. The application's COM classes need only be installed in the HKEY_USERS hive if the application is never used by privileged accounts.
- Drag and drop is not allowed from non-elevated to elevated applications.
Requirements
In order to use the elevation moniker to activate a COM class, the class must be configured to run as the launching user or the 'Activate as Activator' application identity. If the class is configured to run under any other identity, the activation returns the error CO_E_RUNAS_VALUE_MUST_BE_AAA.
The class must also be annotated with a 'friendly' display name that is multilingual user interface (MUI) compatible. This requires the following registry entry:
If this entry is missing, the activation returns the error CO_E_MISSING_DISPLAYNAME. If the MUI file is missing, the error code from the RegLoadMUIStringW function is returned.
Optionally, to specify an application icon to be displayed by the UAC user interface, add the following registry key:
IconReference uses the same format as LocalizedString:

@pathtobinary,-resourcenumber
In addition, the COM component must be signed for the icon to be displayed.
The COM class must also be annotated as LUA-Enabled. This requires the following registry entry:
If this entry is missing, then the activation returns the error CO_E_ELEVATION_DISABLED.
Note that these entries must exist in the HKEY_LOCAL_MACHINE hive, not the HKEY_CURRENT_USER or HKEY_USERS hive. This prevents users from elevating COM classes that they did not also have the privileges to register.
The Elevation Moniker and the Elevation UI
If the client is already elevated, using the elevation moniker will not cause the Elevation UI to display.
How to Use the Elevation Moniker
The elevation moniker is a standard COM moniker, similar to the session, partition, or queue monikers. It directs an activation request to a specified server with the specified elevation level. The CLSID to be activated appears in the moniker string.
The elevation moniker supports the following Run level tokens:
- Administrator
- Highest
The syntax for this is as follows:
The preceding syntax uses the 'new' moniker to return an instance of the COM class specified by guid. Note that the 'new' moniker internally uses the IClassFactory interface to obtain a class object and then calls IClassFactory::CreateInstance on it.
The elevation moniker can also be used to get a class object, which implements IClassFactory. The caller then calls CreateInstance to get an object instance. The syntax for this is as follows:
Sample code
The following code example shows how to use the elevation moniker. It assumes that you have already initialized COM on the current thread.
BIND_OPTS3 is new in Windows Vista. It is derived from BIND_OPTS2.
The only addition is an HWND field, hwnd. This handle represents a window that becomes the owner of the Elevation UI, if applicable.
If hwnd is NULL, COM will call GetActiveWindow to find a window handle associated with the current thread. This case might occur if the client is a script, which cannot fill in a BIND_OPTS3 structure. In this case, COM will try to use the window associated with the script thread.
Over-The-Shoulder (OTS) Elevation
Over-the-shoulder (OTS) elevation refers to the scenario in which a client runs a COM server with an administrator's credentials rather than his or her own. (The term 'over the shoulder' means that the administrator is watching over the client's shoulder as the client runs the server.)
This scenario might cause a problem for COM calls into the server, because the server might not call CoInitializeSecurity either explicitly (that is, programmatically) or implicitly (that is, declaratively, using the registry). For such servers, COM computes a security descriptor that allows only SELF, SYSTEM, and BuiltinAdministrators to makes COM calls into the server. This arrangement will not work in OTS scenarios. Instead, the server must call CoInitializeSecurity, either explicitly or implicitly, and specify an ACL that includes the INTERACTIVE group SID and SYSTEM.
The following code example shows how to create a security descriptor (SD) with the INTERACTIVE group SID.
The following code example shows how to call CoInitializeSecurity implicitly with the SD from the previous code example:
The following code example shows how to call CoInitializeSecurity explicitly with the above SD:
COM Permissions and Mandatory Access Labels
Windows Vista introduces the notion of mandatory access labels in security descriptors. The label dictates whether clients can get execute access to a COM object. The label is specified in the system access control list (SACL) portion of the security descriptor. In Windows Vista, COM supports the SYSTEM_MANDATORY_LABEL_NO_EXECUTE_UP label. SACLs in the COM permissions are ignored on operating systems prior to Windows Vista.
As of Windows Vista, dcomcnfg.exe does not support changing the integrity level (IL) in COM permissions. It must be set programmatically.
The following code example shows how to create a COM security descriptor with a label that allows launch/activation requests from all LOW IL clients. Note that the labels are valid for Launch/Activation and Call permissions. Thus, it is possible to write a COM server that disallows launch, activation or calls from clients with a certain IL. For more information about integrity levels, see the section 'Understanding Windows Vista's Integrity Mechanism' in Understanding and Working in Protected Mode Internet Explorer.
CoCreateInstance and Integrity Levels
The behavior of CoCreateInstance has changed in Windows Vista, to prevent Low IL clients from binding to COM servers by default. The server must explicitly allow such bindings by specifying the SACL. The changes to CoCreateInstance are as follows:
- When launching a COM server process, the IL in the server process token is set to the client or server token IL, whichever is lower.
- By default, COM will prevent Low IL clients from binding to running instances of any COM servers. To allow the bind, a COM server's Launch/Activation security descriptor must contain a SACL that specifies the Low IL label (see the previous section for the sample code to create such a security descriptor).
Elevated Servers and ROT Registrations
If a COM server wishes to register in the running object table (ROT) and allow any client to access the registration, it must use the ROTFLAGS_ALLOWANYCLIENT flag. An 'Activate As Activator' COM server cannot specify ROTFLAGS_ALLOWANYCLIENT because the DCOM service control manager (DCOMSCM) enforces a spoof check against this flag. Therefore, in Windows Vista, COM adds support for a new registry entry that allows the server to stipulate that its ROT registrations be made available to any client:
The only valid value for this REG_DWORD entry is:
The entry must exist in the HKEY_LOCAL_MACHINE hive.
This entry provides an 'Activate As Activator' server with the same functionality that ROTFLAGS_ALLOWANYCLIENT provides for a RunAs server.
Related topics
User Account Control User Oobe Create Elevated Object Server
-->Applies to: Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Server 2019, Windows Server 2016, Windows Server (Semi-annual Channel), Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2
This topic describes how to use Windows Server to deploy Roaming User Profiles to Windows client computers. Roaming User Profiles redirects user profiles to a file share so that users receive the same operating system and application settings on multiple computers.
For a list of recent changes to this topic, see the Change history section of this topic.
Important
Due to the security changes made in MS16-072, we updated Step 4: Optionally create a GPO for Roaming User Profiles in this topic so that Windows can properly apply the Roaming User Profiles policy (and not revert to local policies on affected PCs).
Important
User customizations to Start is lost after an OS in-place upgrade in the following configuration:
- Users are configured for a roaming profile
- Users are allowed to make changes to Start
As a result, the Start menu is reset to the default of the new OS version after the OS in-place upgrade. For workarounds, see Appendix C: Working around reset Start menu layouts after upgrades.
Prerequisites
Hardware requirements
Roaming User Profiles requires an x64-based or x86-based computer; it isn't supported by Windows RT.
Software requirements
Roaming User Profiles has the following software requirements:
If you are deploying Roaming User Profiles with Folder Redirection in an environment with existing local user profiles, deploy Folder Redirection before Roaming User Profiles to minimize the size of roaming profiles. After the existing user folders have been successfully redirected, you can deploy Roaming User Profiles.
To administer Roaming User Profiles, you must be signed in as a member of the Domain Administrators security group, the Enterprise Administrators security group, or the Group Policy Creator Owners security group.
Client computers must run Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Vista, Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2, or Windows Server 2008.
Client computers must be joined to the Active Directory Domain Services (AD DS) that you are managing.
A computer must be available with Group Policy Management and Active Directory Administration Center installed.
A file server must be available to host roaming user profiles.
- If the file share uses DFS Namespaces, the DFS folders (links) must have a single target to prevent users from making conflicting edits on different servers.
- If the file share uses DFS Replication to replicate the contents with another server, users must be able to access only the source server to prevent users from making conflicting edits on different servers.
- If the file share is clustered, disable continuous availability on the file share to avoid performance issues.
To use primary computer support in Roaming User Profiles, there are additional client computer and Active Directory schema requirements. For more information, see Deploy Primary Computers for Folder Redirection and Roaming User Profiles.
The layout of a user's Start menu won't roam on Windows 10, Windows Server 2019, or Windows Server 2016 if they're using more than one PC, Remote Desktop Session Host, or Virtualized Desktop Infrastructure (VDI) server. As a workaround, you can specify a Start layout as described in this topic. Or you can make use of user profile disks, which properly roam Start menu settings when used with Remote Desktop Session Host servers or VDI servers. For more info, see Easier User Data Management with User Profile Disks in Windows Server 2012.
Considerations when using Roaming User Profiles on multiple versions of Windows
If you decide to use Roaming User Profiles across multiple versions of Windows, we recommend taking the following actions:
- Configure Windows to maintain separate profile versions for each operating system version. This helps prevent undesirable and unpredictable issues such as profile corruption.
- Use Folder Redirection to store user files such as documents and pictures outside of user profiles. This enables the same files to be available to users across operating system versions. It also keeps profiles small and sign-ins quick.
- Allocate sufficient storage for Roaming User Profiles. If you support two operating system versions, profiles will double in number (and thus total space consumed) because a separate profile is maintained for each operating system version.
- Don't use Roaming User Profiles across computers running Windows Vista/Windows Server 2008 and Windows 7/Windows Server 2008 R2. Roaming between these operating system versions isn't supported due to incompatibilities in their profile versions.
- Inform your users that changes made on one operating system version won't roam to another operating system version.
- When moving your environment to a version of Windows that uses a different profile version (such as from Windows 10 to Windows 10, version 1607—see Appendix B: Profile version reference information for a list), users receive a new, empty roaming user profile. You can minimize the impact of getting a new profile by using Folder Redirection to redirect common folders. There isn't a supported method of migrating roaming user profiles from one profile version to another.
Step 1: Enable the use of separate profile versions
If you are deploying Roaming User Profiles on computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012, we recommend making a couple of changes to your Windows environment prior to deploying. These changes help ensure that future operating system upgrades go smoothly, and facilitate the ability to simultaneously run multiple versions of Windows with Roaming User Profiles.
To make these changes, use the following procedure.
Download and install the appropriate software update on all computers on which you're going to use roaming, mandatory, super-mandatory, or domain default profiles:
- Windows 8.1, or Windows Server 2012 R2: install the software update described in article 2887595 in the Microsoft Knowledge Base (when released).
- Windows 8 or Windows Server 2012: install the software update described in article 2887239 in the Microsoft Knowledge Base.
On all computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012 on which you will use Roaming User Profiles, use Registry Editor or Group Policy to create the following registry key DWORD Value and set it to
1. For information about creating registry keys by using Group Policy, see Configure a Registry Item.Warning
Incorrectly editing the registry may severely damage your system. Before making changes to the registry, you should back up any valued data on the computer.
Restart the computers.
Step 2: Create a Roaming User Profiles security group
If your environment is not already set up with Roaming User Profiles, the first step is to create a security group that contains all users and/or computers to which you want to apply Roaming User Profiles policy settings.
- Administrators of general-purpose roaming user profiles deployments typically create a security group for users.
- Administrators of Remote Desktop Services or virtualized desktop deployments typically use a security group for users and the shared computers.
Here's how to create a security group for Roaming User Profiles:
Open Server Manager on a computer with Active Directory Administration Center installed.
On the Tools menu, select Active Directory Administration Center. Active Directory Administration Center appears.
Right-click the appropriate domain or OU, select New, and then select Group.
In the Create Group window, in the Group section, specify the following settings:
- In Group name, type the name of the security group, for example: Roaming User Profiles Users and Computers.
- In Group scope, select Security, and then select Global.
In the Members section, select Add. The Select Users, Contacts, Computers, Service Accounts or Groups dialog box appears.
If you want to include computer accounts in the security group, select Object Types, select the Computers check box and then select OK.
Type the names of the users, groups, and/or computers to which you want to deploy Roaming User Profiles, select OK, and then select OK again.
Step 3: Create a file share for roaming user profiles
If you do not already have a separate file share for roaming user profiles (independent from any shares for redirected folders to prevent inadvertent caching of the roaming profile folder), use the following procedure to create a file share on a server running Windows Server.
Note
Some functionality might differ or be unavailable depending on the version of Windows Server you're using.
Here's how to create a file share on Windows Server:
In the Server Manager navigation pane, select File and Storage Services, and then select Shares to display the Shares page.
In the Shares tile, select Tasks, and then select New Share. The New Share Wizard appears.
On the Select Profile page, select SMB Share – Quick. If you have File Server Resource Manager installed and are using folder management properties, instead select SMB Share - Advanced.
On the Share Location page, select the server and volume on which you want to create the share.
On the Share Name page, type a name for the share (for example, User Profiles$) in the Share name box.
Tip
When creating the share, hide the share by putting a
$after the share name. This hides the share from casual browsers.On the Other Settings page, clear the Enable continuous availability checkbox, if present, and optionally select the Enable access-based enumeration and Encrypt data access checkboxes.
On the Permissions page, select Customize permissions…. The Advanced Security Settings dialog box appears.
Select Disable inheritance, and then select Convert inherited permissions into explicit permission on this object.
Set the permissions as described in Required permissions for the file share hosting roaming user profiles and shown in the following screen shot, removing permissions for unlisted groups and accounts, and adding special permissions to the Roaming User Profiles Users and Computers group that you created in Step 1.
Figure 1 Setting the permissions for the roaming user profiles share
If you chose the SMB Share - Advanced profile, on the Management Properties page, select the User Files Folder Usage value.
If you chose the SMB Share - Advanced profile, on the Quota page, optionally select a quota to apply to users of the share.
On the Confirmation page, select Create.
Required permissions for the file share hosting roaming user profiles
| User Account | Access | Applies to |
|---|---|---|
| System | Full control | This folder, subfolders and files |
| Administrators | Full Control | This folder only |
| Creator/Owner | Full Control | Subfolders and files only |
| Security group of users needing to put data on share (Roaming User Profiles Users and Computers) | List folder / read data (Advanced permissions) Create folders / append data (Advanced permissions) | This folder only |
| Other groups and accounts | None (remove) |
@pathtobinary,-resourcenumber
In addition, the COM component must be signed for the icon to be displayed.
The COM class must also be annotated as LUA-Enabled. This requires the following registry entry:
If this entry is missing, then the activation returns the error CO_E_ELEVATION_DISABLED.
Note that these entries must exist in the HKEY_LOCAL_MACHINE hive, not the HKEY_CURRENT_USER or HKEY_USERS hive. This prevents users from elevating COM classes that they did not also have the privileges to register.
The Elevation Moniker and the Elevation UI
If the client is already elevated, using the elevation moniker will not cause the Elevation UI to display.
How to Use the Elevation Moniker
The elevation moniker is a standard COM moniker, similar to the session, partition, or queue monikers. It directs an activation request to a specified server with the specified elevation level. The CLSID to be activated appears in the moniker string.
The elevation moniker supports the following Run level tokens:
- Administrator
- Highest
The syntax for this is as follows:
The preceding syntax uses the 'new' moniker to return an instance of the COM class specified by guid. Note that the 'new' moniker internally uses the IClassFactory interface to obtain a class object and then calls IClassFactory::CreateInstance on it.
The elevation moniker can also be used to get a class object, which implements IClassFactory. The caller then calls CreateInstance to get an object instance. The syntax for this is as follows:
Sample code
The following code example shows how to use the elevation moniker. It assumes that you have already initialized COM on the current thread.
BIND_OPTS3 is new in Windows Vista. It is derived from BIND_OPTS2.
The only addition is an HWND field, hwnd. This handle represents a window that becomes the owner of the Elevation UI, if applicable.
If hwnd is NULL, COM will call GetActiveWindow to find a window handle associated with the current thread. This case might occur if the client is a script, which cannot fill in a BIND_OPTS3 structure. In this case, COM will try to use the window associated with the script thread.
Over-The-Shoulder (OTS) Elevation
Over-the-shoulder (OTS) elevation refers to the scenario in which a client runs a COM server with an administrator's credentials rather than his or her own. (The term 'over the shoulder' means that the administrator is watching over the client's shoulder as the client runs the server.)
This scenario might cause a problem for COM calls into the server, because the server might not call CoInitializeSecurity either explicitly (that is, programmatically) or implicitly (that is, declaratively, using the registry). For such servers, COM computes a security descriptor that allows only SELF, SYSTEM, and BuiltinAdministrators to makes COM calls into the server. This arrangement will not work in OTS scenarios. Instead, the server must call CoInitializeSecurity, either explicitly or implicitly, and specify an ACL that includes the INTERACTIVE group SID and SYSTEM.
The following code example shows how to create a security descriptor (SD) with the INTERACTIVE group SID.
The following code example shows how to call CoInitializeSecurity implicitly with the SD from the previous code example:
The following code example shows how to call CoInitializeSecurity explicitly with the above SD:
COM Permissions and Mandatory Access Labels
Windows Vista introduces the notion of mandatory access labels in security descriptors. The label dictates whether clients can get execute access to a COM object. The label is specified in the system access control list (SACL) portion of the security descriptor. In Windows Vista, COM supports the SYSTEM_MANDATORY_LABEL_NO_EXECUTE_UP label. SACLs in the COM permissions are ignored on operating systems prior to Windows Vista.
As of Windows Vista, dcomcnfg.exe does not support changing the integrity level (IL) in COM permissions. It must be set programmatically.
The following code example shows how to create a COM security descriptor with a label that allows launch/activation requests from all LOW IL clients. Note that the labels are valid for Launch/Activation and Call permissions. Thus, it is possible to write a COM server that disallows launch, activation or calls from clients with a certain IL. For more information about integrity levels, see the section 'Understanding Windows Vista's Integrity Mechanism' in Understanding and Working in Protected Mode Internet Explorer.
CoCreateInstance and Integrity Levels
The behavior of CoCreateInstance has changed in Windows Vista, to prevent Low IL clients from binding to COM servers by default. The server must explicitly allow such bindings by specifying the SACL. The changes to CoCreateInstance are as follows:
- When launching a COM server process, the IL in the server process token is set to the client or server token IL, whichever is lower.
- By default, COM will prevent Low IL clients from binding to running instances of any COM servers. To allow the bind, a COM server's Launch/Activation security descriptor must contain a SACL that specifies the Low IL label (see the previous section for the sample code to create such a security descriptor).
Elevated Servers and ROT Registrations
If a COM server wishes to register in the running object table (ROT) and allow any client to access the registration, it must use the ROTFLAGS_ALLOWANYCLIENT flag. An 'Activate As Activator' COM server cannot specify ROTFLAGS_ALLOWANYCLIENT because the DCOM service control manager (DCOMSCM) enforces a spoof check against this flag. Therefore, in Windows Vista, COM adds support for a new registry entry that allows the server to stipulate that its ROT registrations be made available to any client:
The only valid value for this REG_DWORD entry is:
The entry must exist in the HKEY_LOCAL_MACHINE hive.
This entry provides an 'Activate As Activator' server with the same functionality that ROTFLAGS_ALLOWANYCLIENT provides for a RunAs server.
Related topics
User Account Control User Oobe Create Elevated Object Server
-->Applies to: Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Server 2019, Windows Server 2016, Windows Server (Semi-annual Channel), Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2
This topic describes how to use Windows Server to deploy Roaming User Profiles to Windows client computers. Roaming User Profiles redirects user profiles to a file share so that users receive the same operating system and application settings on multiple computers.
For a list of recent changes to this topic, see the Change history section of this topic.
Important
Due to the security changes made in MS16-072, we updated Step 4: Optionally create a GPO for Roaming User Profiles in this topic so that Windows can properly apply the Roaming User Profiles policy (and not revert to local policies on affected PCs).
Important
User customizations to Start is lost after an OS in-place upgrade in the following configuration:
- Users are configured for a roaming profile
- Users are allowed to make changes to Start
As a result, the Start menu is reset to the default of the new OS version after the OS in-place upgrade. For workarounds, see Appendix C: Working around reset Start menu layouts after upgrades.
Prerequisites
Hardware requirements
Roaming User Profiles requires an x64-based or x86-based computer; it isn't supported by Windows RT.
Software requirements
Roaming User Profiles has the following software requirements:
If you are deploying Roaming User Profiles with Folder Redirection in an environment with existing local user profiles, deploy Folder Redirection before Roaming User Profiles to minimize the size of roaming profiles. After the existing user folders have been successfully redirected, you can deploy Roaming User Profiles.
To administer Roaming User Profiles, you must be signed in as a member of the Domain Administrators security group, the Enterprise Administrators security group, or the Group Policy Creator Owners security group.
Client computers must run Windows 10, Windows 8.1, Windows 8, Windows 7, Windows Vista, Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2, or Windows Server 2008.
Client computers must be joined to the Active Directory Domain Services (AD DS) that you are managing.
A computer must be available with Group Policy Management and Active Directory Administration Center installed.
A file server must be available to host roaming user profiles.
- If the file share uses DFS Namespaces, the DFS folders (links) must have a single target to prevent users from making conflicting edits on different servers.
- If the file share uses DFS Replication to replicate the contents with another server, users must be able to access only the source server to prevent users from making conflicting edits on different servers.
- If the file share is clustered, disable continuous availability on the file share to avoid performance issues.
To use primary computer support in Roaming User Profiles, there are additional client computer and Active Directory schema requirements. For more information, see Deploy Primary Computers for Folder Redirection and Roaming User Profiles.
The layout of a user's Start menu won't roam on Windows 10, Windows Server 2019, or Windows Server 2016 if they're using more than one PC, Remote Desktop Session Host, or Virtualized Desktop Infrastructure (VDI) server. As a workaround, you can specify a Start layout as described in this topic. Or you can make use of user profile disks, which properly roam Start menu settings when used with Remote Desktop Session Host servers or VDI servers. For more info, see Easier User Data Management with User Profile Disks in Windows Server 2012.
Considerations when using Roaming User Profiles on multiple versions of Windows
If you decide to use Roaming User Profiles across multiple versions of Windows, we recommend taking the following actions:
- Configure Windows to maintain separate profile versions for each operating system version. This helps prevent undesirable and unpredictable issues such as profile corruption.
- Use Folder Redirection to store user files such as documents and pictures outside of user profiles. This enables the same files to be available to users across operating system versions. It also keeps profiles small and sign-ins quick.
- Allocate sufficient storage for Roaming User Profiles. If you support two operating system versions, profiles will double in number (and thus total space consumed) because a separate profile is maintained for each operating system version.
- Don't use Roaming User Profiles across computers running Windows Vista/Windows Server 2008 and Windows 7/Windows Server 2008 R2. Roaming between these operating system versions isn't supported due to incompatibilities in their profile versions.
- Inform your users that changes made on one operating system version won't roam to another operating system version.
- When moving your environment to a version of Windows that uses a different profile version (such as from Windows 10 to Windows 10, version 1607—see Appendix B: Profile version reference information for a list), users receive a new, empty roaming user profile. You can minimize the impact of getting a new profile by using Folder Redirection to redirect common folders. There isn't a supported method of migrating roaming user profiles from one profile version to another.
Step 1: Enable the use of separate profile versions
If you are deploying Roaming User Profiles on computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012, we recommend making a couple of changes to your Windows environment prior to deploying. These changes help ensure that future operating system upgrades go smoothly, and facilitate the ability to simultaneously run multiple versions of Windows with Roaming User Profiles.
To make these changes, use the following procedure.
Download and install the appropriate software update on all computers on which you're going to use roaming, mandatory, super-mandatory, or domain default profiles:
- Windows 8.1, or Windows Server 2012 R2: install the software update described in article 2887595 in the Microsoft Knowledge Base (when released).
- Windows 8 or Windows Server 2012: install the software update described in article 2887239 in the Microsoft Knowledge Base.
On all computers running Windows 8.1, Windows 8, Windows Server 2012 R2, or Windows Server 2012 on which you will use Roaming User Profiles, use Registry Editor or Group Policy to create the following registry key DWORD Value and set it to
1. For information about creating registry keys by using Group Policy, see Configure a Registry Item.Warning
Incorrectly editing the registry may severely damage your system. Before making changes to the registry, you should back up any valued data on the computer.
Restart the computers.
Step 2: Create a Roaming User Profiles security group
If your environment is not already set up with Roaming User Profiles, the first step is to create a security group that contains all users and/or computers to which you want to apply Roaming User Profiles policy settings.
- Administrators of general-purpose roaming user profiles deployments typically create a security group for users.
- Administrators of Remote Desktop Services or virtualized desktop deployments typically use a security group for users and the shared computers.
Here's how to create a security group for Roaming User Profiles:
Open Server Manager on a computer with Active Directory Administration Center installed.
On the Tools menu, select Active Directory Administration Center. Active Directory Administration Center appears.
Right-click the appropriate domain or OU, select New, and then select Group.
In the Create Group window, in the Group section, specify the following settings:
- In Group name, type the name of the security group, for example: Roaming User Profiles Users and Computers.
- In Group scope, select Security, and then select Global.
In the Members section, select Add. The Select Users, Contacts, Computers, Service Accounts or Groups dialog box appears.
If you want to include computer accounts in the security group, select Object Types, select the Computers check box and then select OK.
Type the names of the users, groups, and/or computers to which you want to deploy Roaming User Profiles, select OK, and then select OK again.
Step 3: Create a file share for roaming user profiles
If you do not already have a separate file share for roaming user profiles (independent from any shares for redirected folders to prevent inadvertent caching of the roaming profile folder), use the following procedure to create a file share on a server running Windows Server.
Note
Some functionality might differ or be unavailable depending on the version of Windows Server you're using.
Here's how to create a file share on Windows Server:
In the Server Manager navigation pane, select File and Storage Services, and then select Shares to display the Shares page.
In the Shares tile, select Tasks, and then select New Share. The New Share Wizard appears.
On the Select Profile page, select SMB Share – Quick. If you have File Server Resource Manager installed and are using folder management properties, instead select SMB Share - Advanced.
On the Share Location page, select the server and volume on which you want to create the share.
On the Share Name page, type a name for the share (for example, User Profiles$) in the Share name box.
Tip
When creating the share, hide the share by putting a
$after the share name. This hides the share from casual browsers.On the Other Settings page, clear the Enable continuous availability checkbox, if present, and optionally select the Enable access-based enumeration and Encrypt data access checkboxes.
On the Permissions page, select Customize permissions…. The Advanced Security Settings dialog box appears.
Select Disable inheritance, and then select Convert inherited permissions into explicit permission on this object.
Set the permissions as described in Required permissions for the file share hosting roaming user profiles and shown in the following screen shot, removing permissions for unlisted groups and accounts, and adding special permissions to the Roaming User Profiles Users and Computers group that you created in Step 1.
Figure 1 Setting the permissions for the roaming user profiles share
If you chose the SMB Share - Advanced profile, on the Management Properties page, select the User Files Folder Usage value.
If you chose the SMB Share - Advanced profile, on the Quota page, optionally select a quota to apply to users of the share.
On the Confirmation page, select Create.
Required permissions for the file share hosting roaming user profiles
| User Account | Access | Applies to |
|---|---|---|
| System | Full control | This folder, subfolders and files |
| Administrators | Full Control | This folder only |
| Creator/Owner | Full Control | Subfolders and files only |
| Security group of users needing to put data on share (Roaming User Profiles Users and Computers) | List folder / read data (Advanced permissions) Create folders / append data (Advanced permissions) | This folder only |
| Other groups and accounts | None (remove) |
Step 4: Optionally create a GPO for Roaming User Profiles
If you do not already have a GPO created for Roaming User Profiles settings, use the following procedure to create an empty GPO for use with Roaming User Profiles. This GPO allows you to configure Roaming User Profiles settings (such as primary computer support, which is discussed separately), and can also be used to enable Roaming User Profiles on computers, as is typically done when deploying in virtualized desktop environments or with Remote Desktop Services.
Here's how to create a GPO for Roaming User Profiles:
Open Server Manager on a computer with Group Policy Management installed.
From the Tools menu select Group Policy Management. Group Policy Management appears.
Right-click the domain or OU in which you want to setup Roaming User Profiles, then select Create a GPO in this domain, and Link it here.
In the New GPO dialog box, type a name for the GPO (for example, Roaming User Profile Settings), and then select OK.
Right-click the newly created GPO and then clear the Link Enabled checkbox. This prevents the GPO from being applied until you finish configuring it.
Select the GPO. In the Security Filtering section of the Scope tab, select Authenticated Users, and then select Remove to prevent the GPO from being applied to everyone.
In the Security Filtering section, select Add.
In the Select User, Computer, or Group dialog box, type the name of the security group you created in Step 1 (for example, Roaming User Profiles Users and Computers), and then select OK.
Select the Delegation tab, select Add, type Authenticated Users, select OK, and then select OK again to accept the default Read permissions.
This step is necessary due to security changes made in MS16-072.
Important
Due to the security changes made in MS16-072A, you now must give the Authenticated Users group delegated Read permissions to the GPO - otherwise the GPO won't get applied to users, or if it's already applied, the GPO is removed, redirecting user profiles back to the local PC. For more info, see Deploying Group Policy Security Update MS16-072.
Step 5: Optionally set up Roaming User Profiles on user accounts
If you are deploying Roaming User Profiles to user accounts, use the following procedure to specify roaming user profiles for user accounts in Active Directory Domain Services. If you are deploying Roaming User Profiles to computers, as is typically done for Remote Desktop Services or virtualized desktop deployments, instead use the procedure documented in Step 6: Optionally set up Roaming User Profiles on computers.
Note
If you set up Roaming User Profiles on user accounts by using Active Directory and on computers by using Group Policy, the computer-based policy setting takes precedence.
Here's how to set up Roaming User Profiles on user accounts:
In Active Directory Administration Center, navigate to the Users container (or OU) in the appropriate domain.
Select all users to which you want to assign a roaming user profile, right-click the users and then select Properties.
In the Profile section, select the Profile path: checkbox and then enter the path to the file share where you want to store the user's roaming user profile, followed by
%username%(which is automatically replaced with the user name the first time the user signs in). For example:fs1.corp.contoso.comUser Profiles$%username%To specify a mandatory roaming user profile, specify the path to the NTuser.man file that you created previously, for example,
fs1.corp.contoso.comUser Profiles$default. For more information, see Create mandatory user profiles.Select OK.
Note
By default, deployment of all Windows® Runtime-based (Windows Store) apps is allowed when using Roaming User Profiles. However, when using a special profile, apps are not deployed by default. Special profiles are user profiles where changes are discarded after the user signs out:
To remove restrictions on app deployment for special profiles, enable the Allow deployment operations in special profiles policy setting (located in Computer ConfigurationPoliciesAdministrative TemplatesWindows ComponentsApp Package Deployment). However, deployed apps in this scenario will leave some data stored on the computer, which could accumulate, for example, if there are hundreds of users of a single computer. To clean up apps, locate or develop a tool that uses the CleanupPackageForUserAsync API to clean up app packages for users who no longer have a profile on the computer.
For additional background information about Windows Store apps, see Manage Client Access to the Windows Store.
Step 6: Optionally set up Roaming User Profiles on computers
If you are deploying Roaming User Profiles to computers, as is typically done for Remote Desktop Services or virtualized desktop deployments, use the following procedure. If you are deploying Roaming User Profiles to user accounts, instead use the procedure described in Step 5: Optionally set up Roaming User Profiles on user accounts.
You can use Group Policy to apply Roaming User Profiles to computers running Windows 8.1, Windows 8, Windows 7, Windows Vista, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012, Windows Server 2008 R2, or Windows Server 2008.
Note
If you set up Roaming User Profiles on computers by using Group Policy and on user accounts by using Active Directory, the computer-based policy setting takes precedence.
Here's how to set up Roaming User Profiles on computers:
Open Server Manager on a computer with Group Policy Management installed.
From the Tools menu, select Group Policy Management. Group Policy Management will appear.
In Group Policy Management, right-click the GPO you created in Step 3 (for example, Roaming User Profiles Settings), and then select Edit.
In the Group Policy Management Editor window, navigate to Computer Configuration, then Policies, then Administrative Templates, then System, and then User Profiles.
Right-click Set roaming profile path for all users logging onto this computer and then select Edit.
Tip
A user's home folder, if configured, is the default folder used by some programs such as Windows PowerShell. You can configure an alternative local or network location on a per-user basis by using the Home folder section of the user account properties in AD DS. To configure the home folder location for all users of a computer running Windows 8.1, Windows 8, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, or Windows Server 2012 in a virtual desktop environment, enable the Set user home folder policy setting, and then specify the file share and drive letter to map (or specify a local folder). Do not use environment variables or ellipses. The user's alias is appended to the end of the path specified during user sign on.
In the Properties dialog box, select Enabled
In the Users logging onto this computer should use this roaming profile path box, enter the path to the file share where you want to store the user's roaming user profile, followed by
%username%(which is automatically replaced with the user name the first time the user signs in). For example:fs1.corp.contoso.comUser Profiles$%username%To specify a mandatory roaming user profile, which is a preconfigured profile to which users cannot make permanent changes (changes are reset when the user signs out), specify the path to the NTuser.man file that you created previously, for example,
fs1.corp.contoso.comUser Profiles$default. For more information, see Creating a Mandatory User Profile.Select OK.
Step 7: Optionally specify a Start layout for Windows 10 PCs
You can use Group Policy to apply a specific Start menu layout so that users see the same Start layout on all PCs. If users sign in to more than one PC and you want them to have a consistent Start layout across PCs, make sure that the GPO applies to all of their PCs.
To specify a Start layout, do the following:
- Update your Windows 10 PCs to Windows 10 version 1607 (also known as the Anniversary Update) or newer, and install the March 14th, 2017 cumulative update (KB4013429) or newer.
- Create a full or partial Start menu layout XML file. To do so, see Customize and export Start layout.
- If you specify a full Start layout, a user can't customize any part of the Start menu. If you specify a partial Start layout, users can customize everything but the locked groups of tiles you specify. However, with a partial Start layout, user customizations to the Start menu won't roam to other PCs.
- Use Group Policy to apply the customized Start layout to the GPO you created for Roaming User Profiles. To do so, see Use Group Policy to apply a customized Start layout in a domain.
- Use Group Policy to set the following registry value on your Windows 10 PCs. To do so, see Configure a Registry Item.
| Action | Update |
|---|---|
| Hive | HKEY_LOCAL_MACHINE |
| Key path | SoftwareMicrosoftWindowsCurrentVersionExplorer |
| Value name | SpecialRoamingOverrideAllowed |
| Value type | REG_DWORD |
| Value data | 1 (or 0 to disable) |
| Base | Decimal |
- (Optional) Enable first-time logon optimizations to make signing in faster for users. To do so, see Apply policies to improve sign-in time.
- (Optional) Further decrease sign-in times by removing unnecessary apps from the Windows 10 base image you use to deploy client PCs. Windows Server 2019 and Windows Server 2016 don't have any pre-provisioned apps, so you can skip this step on server images.
To remove apps, use the Remove-AppxProvisionedPackage cmdlet in Windows PowerShell to uninstall the following applications. If your PCs are already deployed you can script the removal of these apps using the Remove-AppxPackage.
- Microsoft.windowscommunicationsapps_8wekyb3d8bbwe
- Microsoft.BingWeather_8wekyb3d8bbwe
- Microsoft.DesktopAppInstaller_8wekyb3d8bbwe
- Microsoft.Getstarted_8wekyb3d8bbwe
- Microsoft.Windows.Photos_8wekyb3d8bbwe
- Microsoft.WindowsCamera_8wekyb3d8bbwe
- Microsoft.WindowsFeedbackHub_8wekyb3d8bbwe
- Microsoft.WindowsStore_8wekyb3d8bbwe
- Microsoft.XboxApp_8wekyb3d8bbwe
- Microsoft.XboxIdentityProvider_8wekyb3d8bbwe
- Microsoft.ZuneMusic_8wekyb3d8bbwe
Note
What Is User Oobe
Uninstalling these apps decreases sign-in times, but you can leave them installed if your deployment needs any of them.
Step 8: Enable the Roaming User Profiles GPO
If you set up Roaming User Profiles on computers by using Group Policy, or if you customized other Roaming User Profiles settings by using Group Policy, the next step is to enable the GPO, permitting it to be applied to affected users.
Tip
If you plan to implement primary computer support, do so now, before you enable the GPO. This prevents user data from being copied to non-primary computers before primary computer support is enabled. For the specific policy settings, see Deploy Primary Computers for Folder Redirection and Roaming User Profiles.
Here's how to enable the Roaming User Profile GPO:
- Open Group Policy Management.
- Right-click the GPO that you created and then select Link Enabled. A checkbox appears next to the menu item.
Step 9: Test Roaming User Profiles
Oobe Screen Windows 10
To test Roaming User Profiles, sign in to a computer with a user account configured for Roaming User Profiles, or sign in to a computer configured for Roaming User Profiles. Then confirm that the profile is redirected.
Here's how to test Roaming User Profiles:
Sign in to a primary computer (if you enabled primary computer support) with a user account for which you have enabled Roaming User Profiles enabled. If you enabled Roaming User Profiles on specific computers, sign in to one of these computers.
If the user has previously signed in to the computer, open an elevated command prompt, and then type the following command to ensure that the latest Group Policy settings are applied to the client computer:
To confirm that the user profile is roaming, open Control Panel, select System and Security, select System, select Advanced System Settings, select Settings in the User Profiles section and then look for Roaming in the Type column.
Appendix A: Checklist for deploying Roaming User Profiles
| Status | Action |
|---|---|
| ☐ ☐ ☐ ☐ ☐ | 1. Prepare domain - Join computers to domain - Enable the use of separate profile versions - Create user accounts - (Optional) Deploy Folder Redirection |
| ☐ | 2. Create security group for Roaming User Profiles - Group name: - Members: |
| ☐ | 3. Create a file share for Roaming User Profiles - File share name: |
| ☐ | 4. Create a GPO for Roaming User Profiles - GPO name: |
| ☐ | 5. Configure Roaming User Profiles policy settings |
| ☐ ☐ ☐ | 6. Enable Roaming User Profiles - Enabled in AD DS on user accounts? - Enabled in Group Policy on computer accounts? |
| ☐ | 7. (Optional) Specify a mandatory Start layout for Windows 10 PCs |
| ☐ ☐ ☐ ☐ | 8. (Optional) Enable primary computer support - Designate primary computers for users - Location of user and primary computer mappings: - (Optional) Enable primary computer support for Folder Redirection - Computer-based or User-based? - (Optional) Enable primary computer support for Roaming User Profiles |
| ☐ | 9. Enable the Roaming User Profiles GPO |
| ☐ | 10. Test Roaming User Profiles |
Appendix B: Profile version reference information
Each profile has a profile version that corresponds roughly to the version of Windows on which the profile is used. For example, Windows 10, version 1703 and version 1607 both use the .V6 profile version. Microsoft creates a new profile version only when necessary to maintain compatibility, which is why not every version of Windows includes a new profile version.
The following table lists the location of Roaming User Profiles on various versions of Windows.
| Operating system version | Roaming User Profile location |
|---|---|
| Windows XP and Windows Server 2003 | |
| Windows Vista and Windows Server 2008 | .V2 |
| Windows 7 and Windows Server 2008 R2 | .V2 |
| Windows 8 and Windows Server 2012 | .V3 (after the software update and registry key are applied).V2 (before the software update and registry key are applied) |
| Windows 8.1 and Windows Server 2012 R2 | .V4 (after the software update and registry key are applied).V2 (before the software update and registry key are applied) |
| Windows 10 | .V5 |
| Windows 10, version 1703 and version 1607 | .V6 |
Appendix C: Working around reset Start menu layouts after upgrades
Microsoft Oobe Process
Here are some ways to work around Start menu layouts getting reset after an in-place upgrade:
If only one user ever uses the device and the IT Admin uses a managed OS deployment strategy such as Configuration Manager they can do the following:
Export the Start menu layout with Export-Startlayout before the upgrade
Import the Start menu layout with Import-StartLayout after OOBE but before the user signs in
Note
Importing a StartLayout modifies the Default User profile. All user profiles created after the import has occurred will get the imported Start-Layout.
IT Admins can opt to manage Start's Layout with Group Policy. Using Group Policy provides a centralized management solution to apply a standardized Start Layout to users. There are 2 modes to modes to using Group Policy for Start management. Full Lockdown and Partial Lockdown. The full lockdown scenario prevents the user from making any changes to Start's layout. The partial lockdown scenario allows user to make changes to a specific area of Start. For more info, see Customize and export Start layout.
Note
User made changes in the partial lockdown scenario will still be lost during upgrade.
Let the Start layout reset occur and allow end users to reconfigure Start. A notification email or other notification can be sent to end users to expect their Start layouts to be reset after the OS upgrade to minimized impact.
Change history
User Oobe Create Elevated Object Server Virus
The following table summarizes some of the most important changes to this topic.
Intune User Oobe Create Elevated Object Server
| Date | Description | Reason |
|---|---|---|
| May 1st, 2019 | Added updates for Windows Server 2019 | |
| April 10th, 2018 | Added discussion of when user customizations to Start are lost after an OS in-place upgrade | Callout known issue. |
| March 13th, 2018 | Updated for Windows Server 2016 | Moved out of Previous Versions library and updated for current version of Windows Server. |
| April 13th, 2017 | Added profile information for Windows 10, version 1703, and clarified how roaming profile versions work when upgrading operating systems—see Considerations when using Roaming User Profiles on multiple versions of Windows. | Customer feedback. |
| March 14th, 2017 | Added optional step for specifying a mandatory Start layout for Windows 10 PCs in Appendix A: Checklist for deploying Roaming User Profiles. | Feature changes in latest Windows update. |
| January 23rd, 2017 | Added a step to Step 4: Optionally create a GPO for Roaming User Profiles to delegate Read permissions to Authenticated Users, which is now required because of a Group Policy security update. | Security changes to Group Policy processing. |
| December 29th, 2016 | Added a link in Step 8: Enable the Roaming User Profiles GPO to make it easier to get info on how to set Group Policy for primary computers. Also fixed a couple references to steps 5 and 6 that had the numbers wrong. | Customer feedback. |
| December 5th, 2016 | Added info explaining a Start menu settings roaming issue. | Customer feedback. |
| July 6th, 2016 | Added Windows 10 profile version suffixes in Appendix B: Profile version reference information. Also removed Windows XP and Windows Server 2003 from the list of supported operating systems. | Updates for the new versions of Windows, and removed info about versions of Windows that are no longer supported. |
| July 7th, 2015 | Added requirement and step to disable continuous availability when using a clustered file server. | Clustered file shares have better performance for small writes (which are typical with roaming user profiles) when continuous availability is disabled. |
| March 19th, 2014 | Capitalized profile version suffixes (.V2, .V3, .V4) in Appendix B: Profile version reference information. | Although Windows is case insensitive, if you use NFS with the file share, it's important to have the correct (uppercase) capitalization for the profile suffix. |
| October 9th, 2013 | Revised for Windows Server 2012 R2 and Windows 8.1, clarified a few things, and added the Considerations when using Roaming User Profiles on multiple versions of Windows and Appendix B: Profile version reference information sections. | Updates for new version; customer feedback. |
